Something more worthy of attention from the recent Office of Personnel Management data breach has slipped past the public’s senses. The issue did not only underscore the poor state of cybersecurity in the United States’ federal infrastructure. More significantly, the attack uncovered the reality of a dire lack of cyber experts working for the U.S. […]
OEM Customization in Android Devices Leaves Users Vulnerable to Attacks
As more and more original equipment manufacturers, or OEMs, turn to the practice of customizing their Android version, millions of users are increasingly exposed to malicious attacks.
Is Apple Watch a Failure or Success?
A cloud of doubt was cast over the market performance of the Apple Watch device after the company refused to disclose the revenues and sales figure for the wearable. Is it enough indicator to believe Apple failed to capture a significant foothold in the smart watch market?
Cortana’s deployment in Android confirms Microsoft is losing the Mobile Race
Cortana, Microsoft’s version of Apple’s Siri and Google’s Voice personal assistant, has recently hit the Google Play Store in spite of the Redmond giant’s strategy focused on its own platform.
How Samsung Pay works, and should you use it?
Prior to its worldwide launch, Samsung’s mobile payment system has gone through a beta testing in none other than its home country – South Korea. Korean users have caught the first glimpse of Samsung Pay, how it works and the benefits it offers to consumers. How they reacted to the tool might influence our own […]
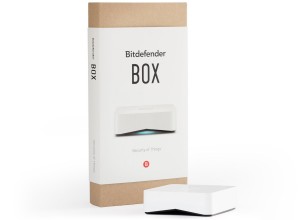
Bitdefender Box: A Security Solution for the Internet of Things
As the Internet of Things continues to gain momentum among individuals and businesses, security experts become increasingly wary of the privacy and security for IoT.