Disclosure: This is a sponsored post, we were compensated to publish this article on our website. 50 years ago, on July 20, 1969, American astronauts Neil Armstrong and Edwin “Buzz” Aldrin landed on the Moon for the first time in human history. It was the 11th manned flight to the Earth’s natural satellite within NASA’s […]
Blog
Wireless Networks and Their Ultimate Benefits
With the passage of time and the spread of technology to almost every facet of life, every electronic device that was made with the intention of making our lives easier elevated to wireless status because wireless equipment enhances the level of comfort – our phones, computers, internet devices, headsets, keyboards, mouse, keys, cars, doors, you […]
10 Tips to Browse Online Safely
Let’s face it. People are exposed to scams every day, whether that’s a telephone scam, a physical scam, or getting scammed online. Identity theft is one of the biggest scams happening on the web right now, and it’s mostly down to the people we meet while using the internet. Mobile internet browsing is on the […]
ROBOQI Automatic Car Phone Holder and Wireless Charger Review
While many modern cars are equipped with a display and an operating system, they are still expensive and the experience is not yet ideal. Therefore, many people prefer using their smartphones with a car phone holder. The ROBOQI that we’re reviewing today is not just a phone mount but also a wireless charger. Let’s check […]
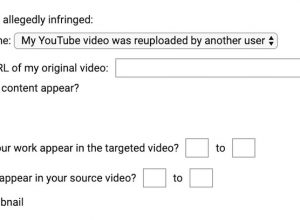
Will YouTube Terminate Your Account for Submitting Copyright Takedown Request?
Recently, we found out a lot of YouTube videos infringing our copyright but they did not show up in the YouTube ‘Copyright Match’ Tool in my account. They’ve overcome the system by using very short portions, messing them up, zooming in a little, or using many still images instead of clips. They used our works […]
Should You Buy a Used Tech Device?
Should I or should I not buy a used gadget is a common question among those who are planning to buy a device for the first time – or upgrading their existing one. Although owning the latest and most sleek gadget is tempting, there are pros of purchasing a used one. As a matter of […]