Before reading the post, I need to disclose that I’ve been a loyal Samsung user for years and I bought the phone for reviewing, so all of my opinions are completely honest.
Blog
How to protect your devices in the Internet of Things world
Connected devices in the age of the Internet of Things continue to expand in number and as this happens, the threat landscape also continues to grow.
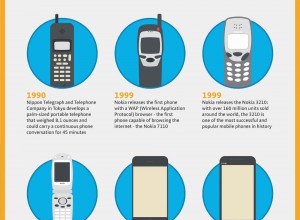
The Evolution of Mobile Phones
It’s more normal now than ever before to have a mobile phone. In fact, many people even have more than one and barely anyone leaves the house without checking they have their mobile on them. But who actually remembers where it all began?
Prevent Visual Hacking with 3M Privacy Filter
This is a sponsored post written by me on behalf of 3M Company for IZEA. All opinions are 100% mine. While high-tech cyber attacks become so popular these days, there is another risk of the old-fashioned physical spying in your office that you shouldn’t ignore, it is also called visual hacking.
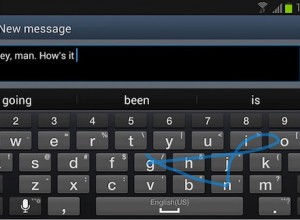
Swift keyboard on Samsung devices exposes users to remote attacks
The problem with built-in apps in mobile devices comes forth when a security hole associated with it presents a real threat to the users.
Apple Watch vs Android Wear: Which way to go?
There are a lot of differences between the Apple Watch and Android Wear operating systems for wearables. These differences are quite noticeable in that both platforms vary tremendously in design. Apple Watch is centered on mobile applications while Android Wear focuses on cloud computing.