Hacking tactics of cyber criminals have dramatically changed: they no longer use malware to infiltrate a network. Instead hackers are resorting to compromised enterprise software to perpetrate their crime.
News
6 Apartment Safety Tips for Renters
Home security is a key cause for worry, especially when living in apartments where you have no control of who can live or enter there. Although there isn’t much you can do to beef up security, put some measures to ensure your belongings and your loved ones are safe. Here are apartment safety tips for […]
Ashley Madison data breach leads to spike in spam emails
The problem with high profile data breach is the domino effect it begets later. Such is the case with the Ashley Madison hack, when spam emails pertaining to the incident have grown in number over the last few weeks after millions of user data were leaked to public domains.
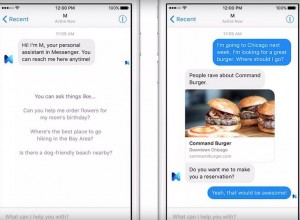
Facebook introduces M, its own personal digital assistant
The competition in the personal digital assistant race has been taken to the next level with Facebook’s introduction of M, its own version of Siri, Google Now and Cortana, but with what it says more enhanced features compared to those of the competitors.
New California Bill could Prevent Google from Pursuing its Drones Project
Unmanned aerial systems are seeing increased interests from various sectors. What with its vast applications, the efficiency and cost-savings provided by drones continue to attract large tech companies such as Google. Amazon and Facebook are also joining onboard.
Browser hijackers: a comprehensive guide
Do you know what a browser hijacker is? If not, you’re in for a nasty surprise. A browser hijacker is a type of malware that takes over your web browser and alters its settings without your permission. This can include changing your default search engine, homepage, and new tab page.